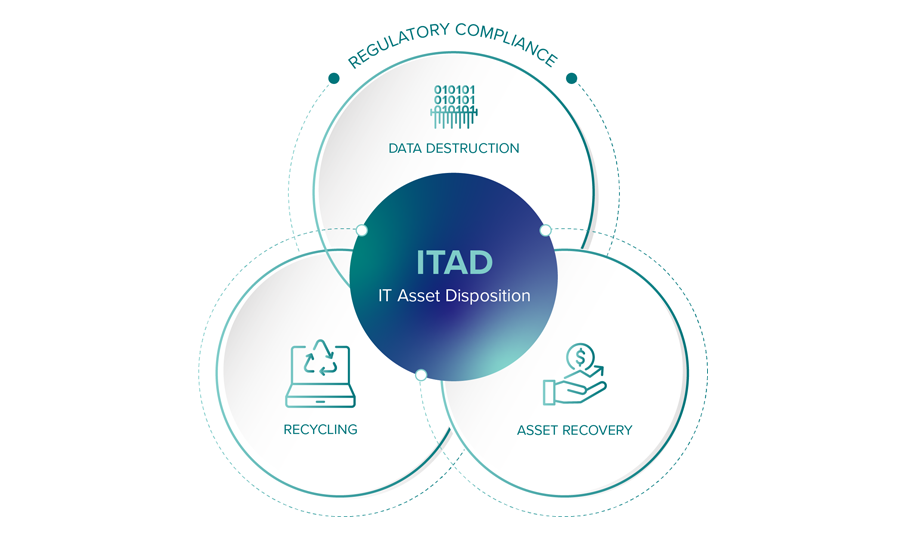
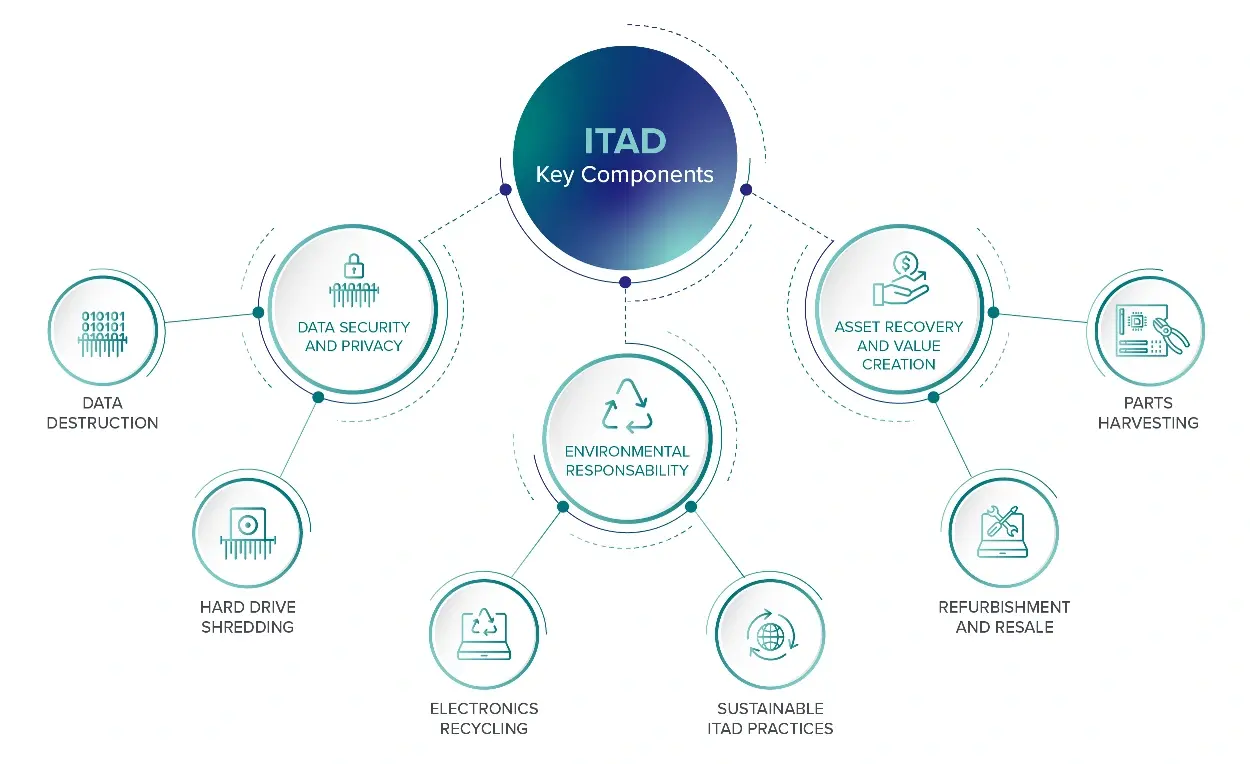
Curious about ITAD services? This article details what ITAD is, what’s included in the ITAD service, and how you can choose the best supplier.

Navigate the complexities of IT asset retirement with guidance from our industry-certified specialists.
As an ITAD company highly rated by Gartner, we offer actionable insights on IT asset disposition, secure data destruction (including hard drive shredding), meeting R2v3, NAID AAA, and NIST compliance standards, sustainable electronics recycling, and maximizing IT equipment buyback value.
Protect your data, ensure regulatory adherence, and optimize your IT lifecycle with our expert support.
ITAD Strategy & Best Practices
Secure Data Destruction, Sanitization, & Hard Drive Shredding
ITAD Compliance & Certifications (e.g., R2, e-Stewards, NAID)
Sustainable E-waste & Electronics Recycling
Maximizing Value: IT Equipment Buyback & Remarketing

Curious about ITAD services? This article details what ITAD is, what’s included in the ITAD service, and how you can choose the best supplier.

HIPAA compliance is essential in disposing health information and hard drives. We share best practices for HIPAA compliance and the consequences of mishandling sensitive information.

HIPAA compliance is essential in disposing health information and hard drives. We share best practices for HIPAA compliance and the consequences of mishandling sensitive information.

Curious about ITAD services? This article details what ITAD is, what’s included in the ITAD service, and how you can choose the best supplier.

Discover the top eight benefits of sustainable ITAD practices. Love your planet and embrace responsible IT asset disposition for a more sustainable future.

Want to maximize IT asset recovery value? Learn when to retire IT equipment, boost resale potential, and choose the right ITAD vendor.
What makes IT asset disposition essential? Learn what ITAD is, why it matters, how to execute it, key risks, and what to consider when choosing a vendor.

ITAMG simplifies server & storage disposition with secure processes, strong compliance, and high recovery value for your used IT assets.

Learn how a robust ITAD policy helps businesses manage outdated IT equipment, ensuring secure data destruction and supporting sustainability initiatives.
Looking for an ITAD vendor? Here’s the importance of choosing the right ITAD vendor, and key factors for evaluating vendors in this comprehensive guide.

Curious about ITAD services? This article details what ITAD is, what’s included in the ITAD service, and how you can choose the best supplier.
Discover the highest-rated ITAD companies based on Gartner Peer Reviews. Explore top providers known for secure data disposal, compliance, and value recovery.

Explore the importance of data destruction in hospitals, key regulations, effective methods, and best practices to ensure ongoing compliance, security, and patient privacy.

Data destruction prevents unauthorized access to sensitive information, protecting against identity theft, financial fraud, and intellectual property theft.

A certified destruction process that meets compliance standards includes a data destruction certificate. Here’s everything you need to know about certification.

Are you worried about donating your devices safely? We share tips on safely donating your old laptop, smartphone, or other devices without compromising data.

NIST 800-88 acts as a guideline for media sanitization. This article covers key guidelines, the consequences of inadequate data destruction, and more.

There are a range of data destruction methods so how do you choose the one one for you? Find out how to choose the right data destruction methods here.

We recently conducted a survey of 3,000 travelers to determine if they felt safe drinking the tap water in specific cities across the U.S. The results are illustrated below. Key Insights from the Survey: Distinct Taste Influencing Perception: Cities like New Orleans...

Back up data, wipe hard drives securely, remove sensitive components, sort materials, and choose a certified recycling partner to ensure legal compliance and data security. Key Takeaways: Recycling computers helps businesses reduce their environmental impact, conserve...

Safeguard data and the environment with smart IT asset disposal practices for businesses.

Create a decommissioning team, define objectives, audit assets, backup and sanitize data, ensure regulatory compliance, dismantle facilities, select ITAD vendors, and conduct a final audit. Key Takeaways: Data center decommissioning involves dismantling the facility...

E-waste contains harmful materials like lead and mercury, contributing to pollution and climate change. Global recycling rates are low, and proper disposal is crucial for environmental health. Key Takeaways: E-waste encompasses discarded electronic devices containing...

To maximize asset recovery value in data center decommissioning, strategically plan ITAD with market analysis, ensure data security, and leverage resale and recycling. Key Takeaways: Understanding the secondary market value of IT assets is crucial for maximizing...

The disposal of old IT equipment in a business is a collective responsibility involving the IT department, legal team, compliance officers, external vendors, and employees. However, it is important that the ultimate responsibility is assigned to a specific party and...

Find out the importance of a data destruction policy and why it’s essential for protecting sensitive information.

Master Service Agreements (MSAs) are not just contractual formalities; they are strategic tools tailored to meet the specific needs of clients. While standard components of an IT Asset Disposition (ITAD) MSA typically encompass asset pick-up, data destruction,...

Choosing the right data destruction provider is key for security and compliance. Explore factors, certifications, methods, and transparency for safe data disposal.

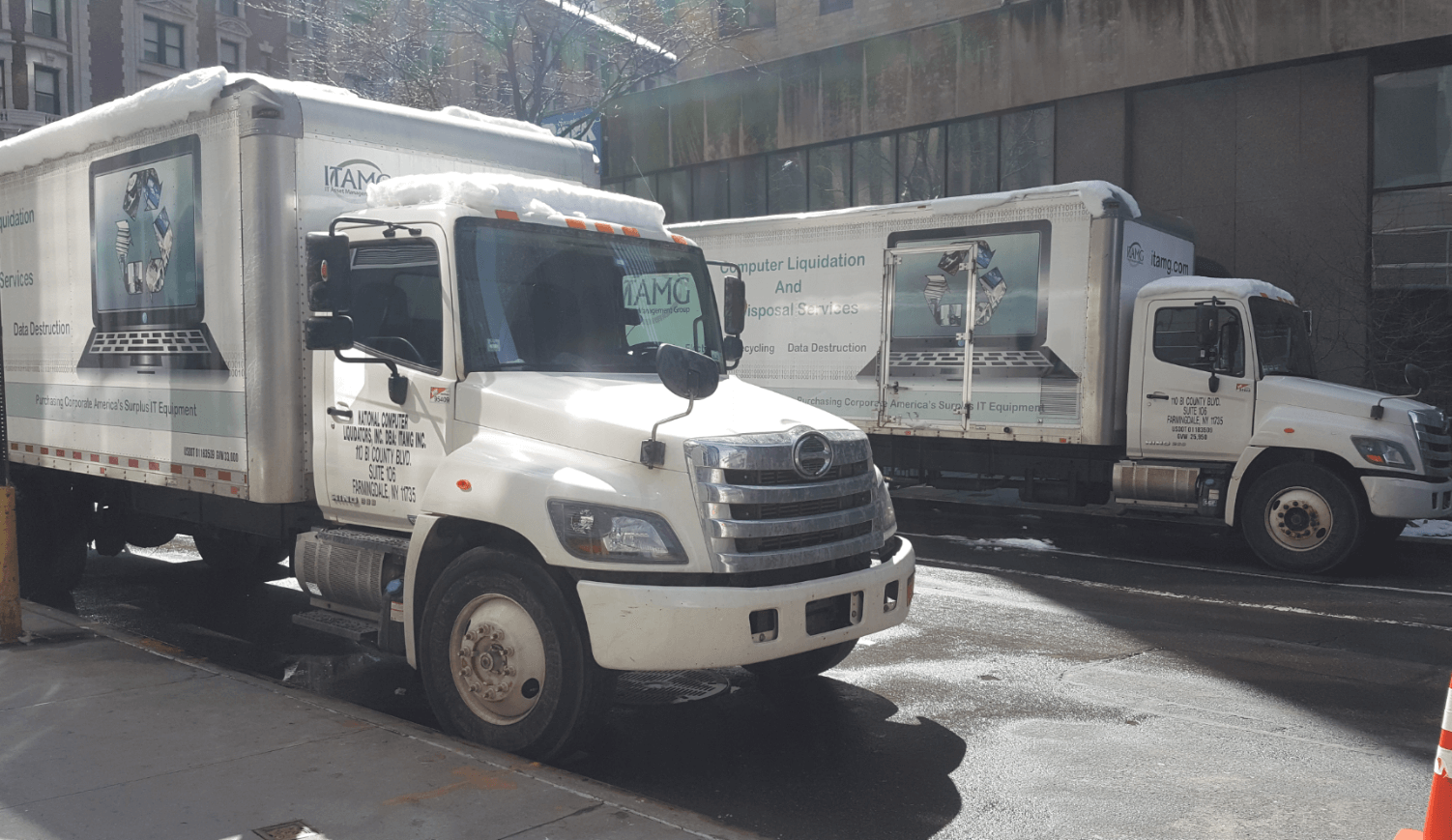
Computer liquidation is the process of selling off surplus or outdated IT assets for cash, focusing on financial return and environmental responsibility. Key Takeaways: Computer liquidation is a strategic process for businesses to convert surplus or outdated IT assets...

To ensure data integrity and access during data center decommissioning, implement meticulous planning, secure data backups, and adhere to strict data destruction protocols. Key Takeaways: Data center decommissioning requires meticulous planning to ensure data...

Shredded hard drives are reduced to tiny fragments, making data recovery an unreasonable endeavor. The waste remains are then recycled for precious metals and commodity recovery. Key Takeaways: Shredded hard drives are reduced to tiny particles, making data recovery...

Post-migration optimization in the cloud involves monitoring KPIs, fine-tuning performance, leveraging cloud-native tools, and balancing resources for cost-effective, efficient operations. Key Takeaways: Post-migration cloud optimization involves continuous monitoring...

Data center decommissioning case studies reveal that meticulous planning, compliance with data security laws, and project coordination are key to successful, secure, and eco-friendly project execution. Key Takeaways: Conducting a thorough site survey and comprehensive...

To overcome technical debt during cloud migration, assess and prioritize debt, adopt incremental modernization strategies, and leverage automation, re-platforming, and IT asset disposal. Key Takeaways: Assess and prioritize technical debt before cloud migration to...

Migrating to the cloud requires adapting Governance, Risk, and Compliance (GRC) strategies to address new risks, ensure compliance, and manage governance in a dynamic environment. Key Takeaways: Governance, Risk, and Compliance (GRC) must be integrated into the cloud...

As businesses look towards spring, the concept of cleaning out and refreshing becomes not just a personal endeavor but a critical business operation—especially when it comes to Information Technology Asset Disposition (ITAD). Regular IT asset refreshes and disposals...

To record IT asset disposal, identify assets, choose disposal timing, document transactions, and adjust accounting records, ensuring legal compliance and data destruction. Key Takeaways: Properly identifying and timing the disposal of IT assets is crucial for...

Common business devices that become e-waste include printers, copiers, desktops, laptops, servers, smartphones, tablets, routers, switches, modems, and external hard drives. Key Takeaways: Office electronics such as printers, copiers, and fax machines often become...

The IT asset decommissioning process involves securely retiring IT equipment, ensuring data security, regulatory compliance, cost savings, and environmental responsibility. Key Takeaways: IT asset decommissioning is a critical phase in the lifecycle management of...

Businesses should responsibly recycle computers to conserve resources, reduce emissions, and manage hazardous waste, enhancing brand image and meeting CSR goals. Key Takeaways: Recycling computers helps businesses conserve resources, reduce greenhouse gas emissions,...

Businesses generate e-waste, such as outdated computers, mobile devices, printers, and servers, which pose environmental, data security, and legal challenges. Effective e-waste management can offer economic benefits and enhance brand reputation. Key Takeaways:...

E-waste solutions include designing sustainable products, implementing take-back programs, choosing certified recyclers, and fostering a circular economy to minimize waste. Key Takeaways: E-waste, comprising discarded electronics with batteries or plugs, poses...

E-waste contains toxic chemicals and heavy metals that can cause organ damage, cancer, and immediate injuries like cuts and respiratory issues. Key Takeaways: E-waste contains harmful substances like lead, mercury, and cadmium, which can cause serious health issues...

E-waste poses serious environmental risks, releasing toxic chemicals and greenhouse gases, contaminating soil and water, and impacting human health and ecosystems. Key Takeaways: E-waste, consisting of discarded electronics like computers and smartphones, releases...

Quick Answer: E-waste recycling involves collecting, sorting, and processing discarded electronics to recover commodities and safely dispose of hazardous substances, essential for sustainable business operations. Key Takeaways: E-waste recycling is essential for...
The stability and security offered by long-term vendor relationships cannot be overstated. Master Service Agreements (MSAs) serve as key instruments in not just forging, but also future proofing these partnerships. MSAs go beyond mere contractual obligations, they are...

Master Service Agreements (MSAs) play a pivotal role in mitigating risks and ensuring compliance, acting as robust shields that protect customers and their ITAD providers. These agreements are meticulously designed to encompass a wide range of legal, operational, and...

Introduction to Master Service Agreements in ITAD In the realm of IT Asset Disposition (ITAD), the establishment of a clear and structured relationship between service providers and their clients is paramount. This is where Master Service Agreements (MSAs) come into...

Striking a balance between secure media destruction and promoting the circular economy is crucial. Achieving this equilibrium is not only about protecting sensitive data but also about contributing responsibly to environmental sustainability. How can organizations...

In an era where sustainability is no longer a choice but a necessity, the way we view and manage electronic waste (e-waste) is undergoing a fundamental shift. The rapid growth of e-waste calls for innovative approaches to e-waste management, steering us towards a more...

The digital revolution, while driving global progress, has inadvertently given rise to a burgeoning environmental challenge: electronic waste (e-waste). The rapid turnover of electronic devices, driven by constant technological advancements and consumer demand for the...

Talking about giving often sounds cliché or disingenuous. We've all heard about the importance of giving back countless times. However, the reason this message persists is rooted in the profound impact that giving can have on the lives of those in need. The good...

Environmental, Social, and Governance (ESG) goals are fundamental to shaping a sustainable and equitable future. The path to achieving these goals is multifaceted and requires innovative approaches. One of the most impactful steps a company can take is through the...

Access to technology is not just about staying connected; it's a lifeline to education, economic opportunities, and a brighter future. Yet, for many low-income families, this lifeline remains out of reach. The digital divide is a chasm that separates those with access...
Learn about data destruction and the two primary methods: data erasure and hard drive shredding. Stay informed on IT asset disposal topics. Subscribe now!

When it comes to IT asset disposition (ITAD), trust is paramount. But where do you draw the line? There are two pivotal questions to ponder: Where is your line of demarcation? What influences the placement of that line? For many, this line is driven by either...

Last week the Department of the Treasury OCC levied a $60 million dollar fine to Morgan Stanley for data breaches that occurred from poorly managed IT asset disposition projects associated to data center decommissioning activities in 2016 and additional disposal...
We here at IT Asset Management Group (ITAMG) regularly come across regional organizations such as universities, hospitals, media companies and local banks that are engaged with disposal providers that ship their retired IT equipment several hundred or even a thousand...

As a NAID Certified Secure Destruction Specialist my goal is to offer information security and compliance professionals objective advice backed by experience, industry best practices and a keen knowledge of the applicable regulatory requirements. When working with...

Last week Arrow Electronics Inc. announced that it would be shutting the doors on its IT asset disposition service business leaving the industry dumbfounded and thousands of customers concerned with how to proceed with their day to day disposal requirements. Although...

When we fail in life, especially at our security, we tend to overreact and make quick and sweeping changes. If you leave your door open and your home is burglarized, moving out of your neighborhood or installing a state of the art security system may be an irrational...

It’s time your IT asset disposal program manager ditches a murky understanding of DoD data destruction(Department of Defense 5220.22-M) by adding a clearer understanding of the NIST 800-88 (National Institute of Standards and Technology 800-88 Guidelines for Media...

If your IT department generates valuable surplus computer equipment whether through a regular refresh project, office relocation, staff reduction or merger it will be helpful to understand how to bid out an IT asset disposal project to computer liquidators.We suggest...

Evaluating an IT liquidation provider to purchase your corporate IT equipment can be a difficult task to accomplish. There are a good deal of variables that can lead an IT manager down a path where he or she will be unable to accurately evaluate competitive...

Proper handling of end of life computer equipment and electronic media is critical to avoiding costly data breaches and debilitating exposures to your business and client data. Your options for hard drive disposal should not be limited by archaic security...
Many companies in the electronics recycling and IT asset disposal industry utilize scare tactics and try to focus a buyer’s attention on false narratives to win new clients and increase profitability of contracts. We believe in transparency and educating our clients....

At ITAMG we have been advising our clients on the big picture best practices for IT asset management, computer recycling, and secure data erasure. The following are five specific tips to help you make the most of your IT asset disposal program. 1) Communicate...

Part 2: Documenting a Site Visit to an IT Asset Disposal Service Provider In this second installment of best practices for vetting a disposal vendor and documenting a process for electronic waste disposition IT Asset Management Group (ITAMG) is advising organizations...

Part 1: Instituting a Master Service Agreement IT Asset Management Group (ITAMG) will be publishing multiple blog posts to prepare organizations for audits around computer equipment disposal, environmental compliance, and data security for end of life media and...

If your company’s end users rely on Windows XP you are probably aware that on April 8th, 2014 Microsoft support for XP will end. The reason for this decision is discussed in this post by Elephant Outlook “Microsoft to Windows XP User – Your Operating System is a Major...

Perhaps the most common question people ask IT Asset Management Group is how do we figure out what surplus IT equipment is worth? In order for ITAMG to provide our clients with bids, proposals, and projections for surplus and end of life computer equipment, we...

Government agencies, corporations, and various institutions are taking measures to improve IT asset management and disposition practices in order to mitigate risk of a data breach, achieve environmental initiatives, and ensure optimal financial performance. The...
The best place to start is the beginning of course, regardless if this is your first IT Asset Disposal (ITAD) project or your hundredth. An investment in knowledge pays the best interest and knowing the “Four Knows” can help return that interest for your surplus IT...

IT Asset Management Group (ITAMG), a leading provider of IT asset disposal, data destruction and electronics recycling services, has joined the EPEAT Champion program. EPEAT is the definitive global rating system for greener electronics. Becoming an EPEAT...
E-waste is on the rise and the impending result will impact us all. According to a USA Today article referencing a UN Study, “The mountain of refrigerators, cellphones, TV sets and other electrical waste disposed of annually worldwide is forecast to grow by a third by...

Project management is a critical component in any IT project yet end of life disposal process is often lacking the proper amount of attention. Proper IT disposal planning will minimize data security risks and cleanly close out the life cycle of computer equipment with...

What happens when end use computing, mobile devices and data center infrastructure reach the end of its useful life in the enterprise environment? It turns into a major business liability. Each week, vast amounts of hardware is discarded by corporations large and...

Growing up watching someone talk into their watch always looked pretty cool. Now with the Samsung Galaxy Gear that high-tech, talk into your watch age is here. Samsung has been winning praise for their ads which speak to that TV viewing audience. An article on...
“Don’t panic, it’s only a data breach.” Are those words that you would ever hear? Certainly not, because when there is a data breach, while panic may not be the optimal reaction, it is more often than not the reaction. A data breach can cause shock waves through a...

An IT Manager takes on a diverse role that encompasses technical challenges, analyzing information, staffing, conflict resolution, strategic planning, developing budgets, and even data center management. Both the technical and management components require your...

Ever hear of this thing called “big data”? It is hard to visualize reams of information and how to make them useful, especially when it comes to understanding all the different kinds of data breaches and industries most effected. Creative engineers and information...
ITAM stands for IT Asset Management, but there is often a lot of confusion when talking to vendors that name solutions after industry terms, let alone a a certain company that just so happens to be named IT Asset Management Group. All too often acronyms confuse...

The government, corporations, and citizens in the United States have a higher awareness than ever before for the necessity to properly recycle electronic waste. Although there have been positive results from educating and regulating the electronic waste producers,...

Would you believe that a large number of desktop virtualization projects get to roughly about 30% completion and then never reach production? An even greater number fall apart prior to even reaching a small scale pilot stage. What makes ITAMG an expert to even share a...
Written By Peter Fleming of Soundview IT Solutions In the middle of 2011 a Connecticut based hedge fund announced their founder was retiring and the fund would subsequently be closing its doors. Among the myriad of issues the hedge fund faced, one was definitively...
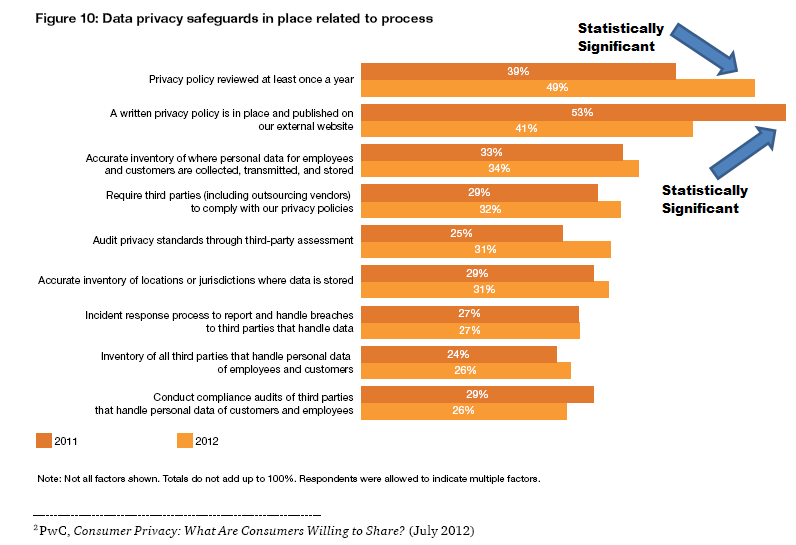
For many businesses, information and hardware asset security has become a daily concern. IT Asset Management Group would like to highlight a chart from PricewaterhouseCoopers 15th annual Global State of Information Security® Survey that illustrates the statistical...